GSA Raises the Bar on Cybersecurity for Federal Contractors
- Contributor
- Allison D. Ward
May 1, 2026
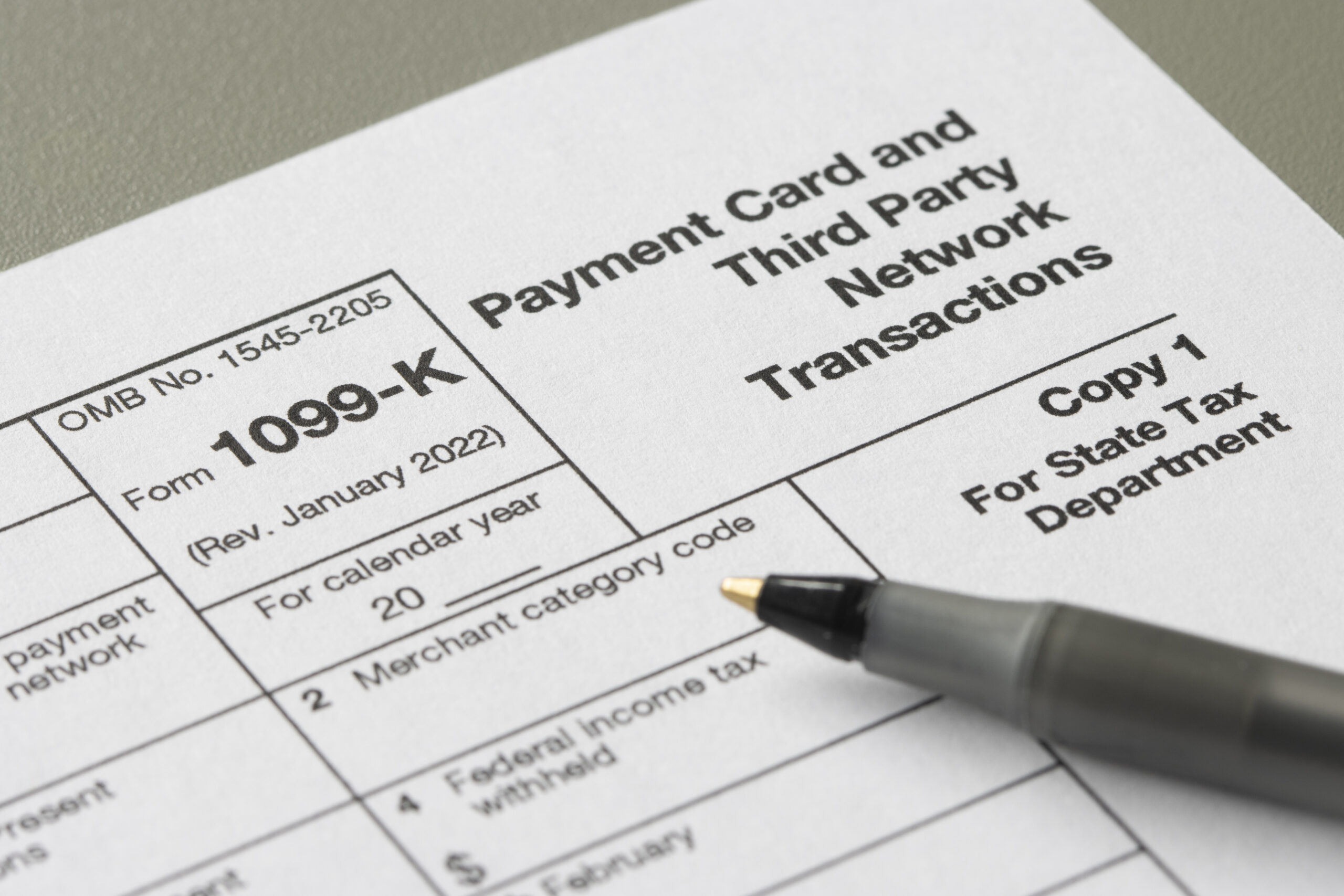
In January 2026, the General Services Administration (GSA) updated its IT security guidance, significantly raising cybersecurity expectations for contractors that handle Controlled Unclassified Information (CUI) in nonfederal systems and processes. While the update does not require formal CMMC certification, it does include independent assessment requirements and review by GSA’s Office of the Chief Information Security Officer (OCISO) prior to system use. Its structure and control expectations closely align with the Department of Defense’s (DoD) Cybersecurity Maturity Model Certification (CMMC) framework.
This shift is notable because it originated with GSA, which oversees procurement for civilian agencies, rather than the DoD. The CMMC has traditionally served as the DoD’s framework for measuring and enforcing cybersecurity practices among contractors that handle sensitive government information. While GSA’s updated guidance is not identical to CMMC, it reflects a comparable move toward more structured, NIST-aligned cybersecurity expectations in the civilian federal marketplace.
Immediate Implementation and Industry Response
Unlike the DoD, which rolled out CMMC in phases, GSA implemented the revised guidance immediately. The new requirements apply immediately to new solicitations and contract awards, depending on the contracting officer’s decision.
The updated guidance establishes clearer expectations for contractors who handle CUI in nonfederal systems. These rules include multi-factor authentication, encryption, independent assessments, and ongoing risk monitoring. The framework aligns with NIST Special Publication 800-171 r3 and references NIST SP 800-172 r3 in draft form, signaling a move toward more structured, auditable cybersecurity requirements.
And while many industry participants were familiar with the underlying standards, many were surprised by the speed and scope of implementation. Many contractors thought civilian agencies would take longer to adopt similar rules. Instead, GSA’s move shows that civilian agencies are acting more quickly to align with the cybersecurity expectations already in place for defense contracts.
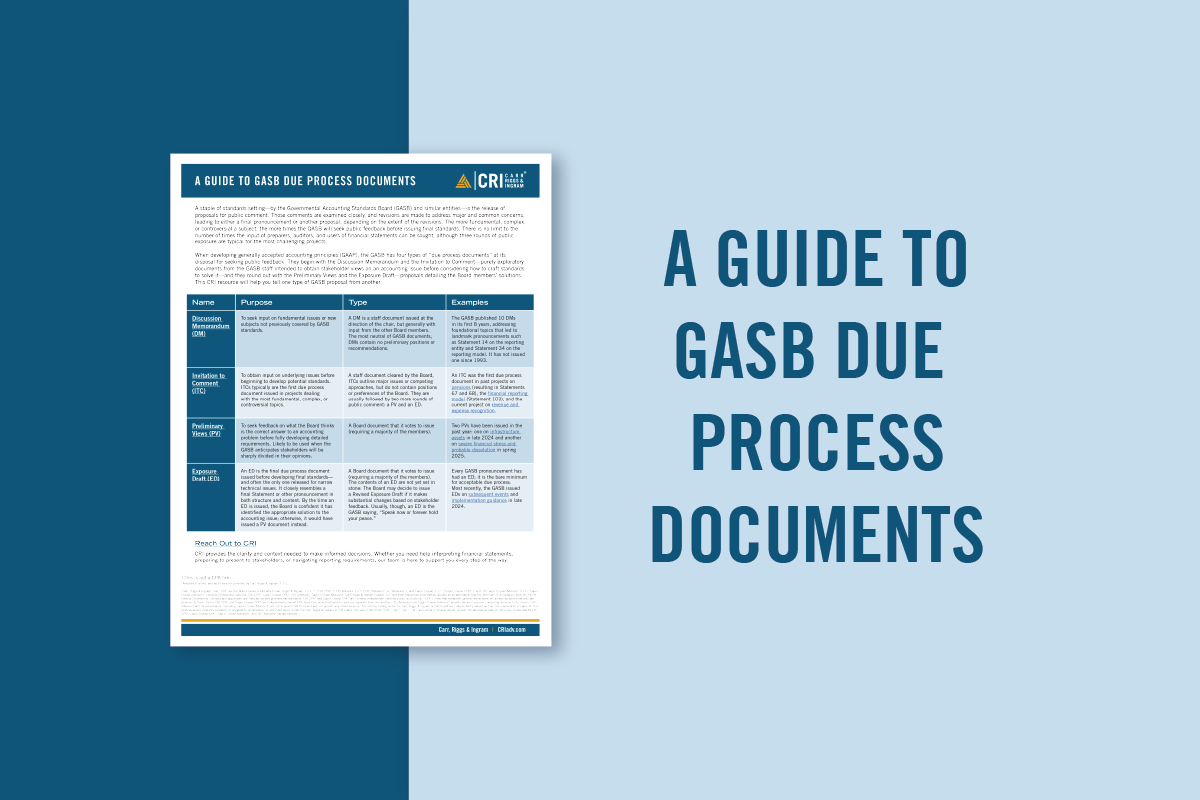
How GSA’s Guidance Compares to CMMC
CMMC Level 2 is based on NIST SP 800-171 r2, which includes 110 security requirements across 14 control families. GSA’s updated guidance appears to align more closely with NIST SP 800-171 r3, which includes many similar cybersecurity concepts but also reflects notable updates from the earlier version. As a result, the technical, administrative, and operational expectations may feel familiar to contractors preparing for CMMC, but the requirements should not be treated as identical.
The main difference between the two frameworks is how they are enforced. While GSA does not follow the same formal third-party certification model used under CMMC, its guidance includes an assessment and approval process prior to system use. Contractors are expected to undergo an independent assessment as part of their submission to obtain a Memorandum of Record from GSA’s Office of the Chief Information Security Officer (OCISO), with reassessments required every three years. Compliance is then reinforced through contract terms, documentation reviews, and continued oversight after award. While this approach differs from CMMC’s certification structure, it still introduces a level of rigor that contractors should not underestimate.
Rising Enforcement Risk and Broader Federal Alignment
As federal agencies strengthen cybersecurity requirements, the exposure to enforcement continues to grow. In fiscal year 2025, the U.S. Department of Justice reported $6.8 billion in settlements and judgments under the False Claims Act, with cybersecurity-related matters representing an increasing share of enforcement activity.
Recent settlements demonstrate the potential consequences when contractors fail to implement required controls or inaccurately represent their compliance posture. In one case, a federal contractor paid millions of dollars to resolve allegations that it did not implement mandated cybersecurity safeguards while continuing to bill government agencies. These actions reflect the government’s heightened focus on ensuring contractors meet their cybersecurity obligations and accurately report compliance.
Under the False Claims Act, contractors that knowingly misstate their cybersecurity practices may face substantial financial penalties, contract termination, adverse performance evaluations, and reputational harm. As requirements become more clearly defined and actively enforced, contractors that depend on federal revenue may experience increased scrutiny of both their control environments and their compliance representations.
At the same time, GSA’s update is unlikely to remain isolated. Agencies that manage significant volumes of sensitive data, oversee critical infrastructure, or rely heavily on contractor support already align with NIST frameworks and face similar risk pressures. By revising its guidance ahead of broader Federal Acquisition Regulation changes, GSA has established a model that other civilian agencies may follow. The result could be a more consistent cybersecurity baseline across both defense and civilian procurement environments.
What This Means for Contractors and Executives
GSA did not invent a new set of cybersecurity rules. Instead, it made existing standards more common and expanded their use. CMMC-level expectations are now spreading beyond defense contracts and are becoming the standard across the federal market. This change is especially important for companies that work with both defense and civilian agencies. This includes systems integrators, managed service providers, cloud providers, and professional services firms that use GSA contracts.
For executives and boards, cybersecurity compliance is now closely linked to being able to win contracts, keep revenue steady, and manage risk. Organizations that embed NIST-aligned controls into their policies, documentation, and daily operations may be better prepared to compete as compliance requirements become stricter. Those who see cybersecurity as just paperwork may face more scrutiny and risk losing contracts.
Assessing Readiness in a Changing Cybersecurity Environment
The federal government’s expectations for contractor cybersecurity are changing, and the gap between defense and civilian enforcement is shrinking. As agencies focus more on documented, auditable cybersecurity controls, contractors may want to review how their current practices align with NIST-based frameworks and contract requirements.
If your organization works with federal contracts or is reviewing its cybersecurity readiness because of new GSA and CMMC expectations, your CRI advisor can help you understand your risks and how these changes might affect your compliance. Reach out to your CRI advisor to talk about your situation and plan your next steps.